Products
Solutions
Resources

A compliance management workflow is the operational backbone that determines whether your organization can withstand regulatory scrutiny or scrambles to respond after the fact. For general counsels and corporate secretaries at large public companies, the challenge is no longer building a compliance program from scratch. It is redesigning workflows that buckle under the weight of overlapping frameworks, cross-departmental handoffs and regulatory environments that shift faster than manual processes can track.
The enforcement landscape is volatile — and that volatility itself is a compliance risk. In FY 2024, the SEC reported 583 enforcement actions, while DOJ and SEC FCPA sanctions exceeded $1.5 billion. FY 2025 brought a sharp reversal: standalone SEC enforcement actions fell 27% to 313 amid an administration change and a temporary FCPA enforcement pause.
But reduced federal activity does not mean reduced compliance risk, it means enforcement priorities are shifting, investigation pipelines are building and organizations that relaxed controls during the pause face compounding exposure when activity resumes.
Meanwhile, Diligent Institute's Q4 Business Risk Index found that 44% of organizations cite cross-functional coordination as an area needing improvement, the same coordination that compliance workflows depend on to function.
This guide provides a sequential implementation path to build or redesign a compliance management workflow that holds up under audit committee review, survives regulatory inquiry and absorbs new frameworks without requiring a rebuild.
This guide covers:
A compliance management workflow is a repeatable, documented sequence of steps that moves from regulatory identification through control implementation to monitoring, reporting and remediation. It differs from ad hoc compliance in one fundamental way: Architecture.
Ad hoc compliance responds episodically. A new regulation surfaces, a team scrambles to address it, and documentation happens after the fact. A structured workflow embeds compliance into ongoing business operations with defined ownership, standardized processes and continuous improvement cycles.
The distinction matters because regulators evaluate exactly this. The DOJ's evaluation of corporate compliance programs asks three questions that prosecutors weigh during enforcement investigations: Is the compliance program well-designed? Is it being applied in good faith? Does it work in practice? Organizations running episodic, disconnected compliance responses — regardless of how well-resourced those responses are — struggle to answer "yes" to all three.
Existing workflows break down at enterprise scale for predictable, structural reasons — not because teams lack effort or resources.
The solution is not adding more compliance staff or more documentation. It is redesigning the underlying architecture so each new requirement adds incrementally less burden because it connects to existing integrated infrastructure.
"Cross-functional coordination is key for operating in a world where top risks are interdependent and self-amplifying," says Kira Ciccarelli, Senior Manager of Research at Diligent Institute.
Building an enterprise compliance workflow requires sequential implementation. Each step depends on the one before it. Skip the foundational work and the downstream steps become exercises in documentation rather than operational compliance.
The framework below draws on the COSO internal control framework and NIST 800-39 risk management methodology, adapted for multi-jurisdictional enterprise environments.
Build a comprehensive regulatory inventory that becomes your operating baseline. Your mapping should capture every obligation across every jurisdiction where the organization operates, map each obligation to impacted business units, processes and systems, identify overlaps across jurisdictions to enable control reuse and flag conflicts across jurisdictions to force governance decisions.
The output is a regulatory universe map — a living document that serves as the foundation for everything that follows. Without this baseline, every subsequent step operates on assumptions rather than documented requirements.
Every compliance obligation needs a named owner — not a department, a person. Use a RACI or RASCI matrix to remove ambiguity at handoffs:
Without named accountability at each transition point, ownership defaults to no one. This is the single most common root cause of compliance failures that surface during audits — not missing controls, but unclear ownership of existing controls.
Structure ownership using the Three Lines model: First-line management owns controls. Second-line compliance and risk functions provide oversight. Third-line internal audit delivers independent assurance.
Ensure internal audit's authority and responsibilities are formally defined and board-approved in line with the IIA's Global Internal Audit Standards, and that the chief compliance officer has direct board reporting lines so escalation authority works across business unit boundaries.
This is where most organizations create unnecessary work. Managing SOX, GDPR, HIPAA and ISO 27001 as separate compliance programs generates exponential workload growth. The alternative: Design your control environment once, then map it to multiple frameworks.
Start by mapping regulatory requirements to established frameworks — COSO for internal control, NIST for cybersecurity. Then identify where a single control can satisfy requirements across multiple frameworks simultaneously. For security and technology controls, adopt a common language such as NIST 800-53 to improve consistency across teams and documentation.
A common control strategy prevents your compliance workload from scaling exponentially with each new framework. When a new regulation enters scope, you map it to existing controls first, then build only what is missing.
Embed controls into existing business processes rather than creating parallel compliance workflows. A complete control environment typically includes three types:
For each control, document the specific regulatory requirement it satisfies, the business process it operates within, how frequently it operates and the evidence it produces. Then build control matrices that link every requirement from your regulatory universe map to at least one implemented control. If a requirement has no corresponding control, that gap needs to be prioritized.
Documentation is not a step that happens after compliance work is done — it must be embedded in the control itself. Every control execution should automatically generate evidence that meets the PCAOB AS 1105 standard for audit evidence: relevant to the specific assertion being tested, reliable in its source, sufficient in quantity and appropriate in quality.
Design evidence collection to satisfy the most stringent retention requirement across all applicable frameworks for your organization. The SEC's baseline seven-year retention requirement is a useful floor. Implement audit trails that capture user actions, timestamps, device information and both successful and failed access attempts. Ensure your electronic recordkeeping approach aligns with applicable SEC recordkeeping rules.
The goal: When auditors request evidence, it already exists in a format they can use. No scrambling, no reconstructing and no asking three departments to produce the same document in different formats.
Move from periodic audits to continuous monitoring. The distinction matters because annual or semi-annual testing captures a snapshot, not ongoing control effectiveness. Tier your monitoring cadences based on risk so testing effort matches exposure:
The ultimate benchmark: Audit preparation should be a non-event. If your monitoring cadences are working, the evidence, exceptions and remediation records already exist before anyone asks for them.
Define clear escalation paths so compliance issues move from identification to resolution without stalling at departmental boundaries. Effective escalation requires organizational authority backed by senior management, as outlined in the OFAC compliance framework.
Build protocols that specify severity classifications — including what qualifies as "material" — response timeframes by severity, remediation owners and required approvals and verification requirements to close issues.
Then connect the workflow to board and audit committee reporting. Design your reporting cadence to deliver quarterly reviews at minimum, with annual program maturity assessments and the ability to escalate material findings outside the standard cycle. Audit committees should receive the compliance metrics outlined below, not narrative summaries that obscure operational reality.
Measurement is the feedback loop that prevents compliance workflows from decaying into checkbox exercises. Without quantified reporting, audit committees receive narrative assurance rather than the operational visibility they need to fulfill their oversight obligations.
Translate workflow performance into a focused set of metrics that can be trended over time:
Build these metrics into your standard reporting cadence so measurement becomes infrastructure, not a special request. Audit committees increasingly expect quantified compliance data they can compare across quarters.
The workflow challenges documented above — manual evidence collection, multi-framework duplication, regulatory change tracking across jurisdictions and disconnected board reporting — are exactly the operational bottlenecks that Diligent's compliance infrastructure addresses.
Diligent’s IT Compliance supports centralized compliance monitoring across more than 75 frameworks, including HIPAA, ISO 27001, NIST, FedRAMP, SOC 2 and GDPR. The platform's cross-framework control mapping directly solves the redundant control problem from Step 3 — organizations map regulations and standards against common control frameworks, maintaining evidence once rather than duplicating work across every program. Through Regology integration, IT Compliance provides automated regulatory intelligence with continuously updated regulation libraries.
As requirements change across jurisdictions, AI surfaces relevant updates specific to each organization's obligations, eliminating the manual tracking that creates the regulatory change response delays measured in Step 7.
Policy Manager automates the attestation and approval workflows that compliance teams otherwise manage through manual follow-up — the exact handoff gaps identified in Step 2 as a root cause of compliance failures.
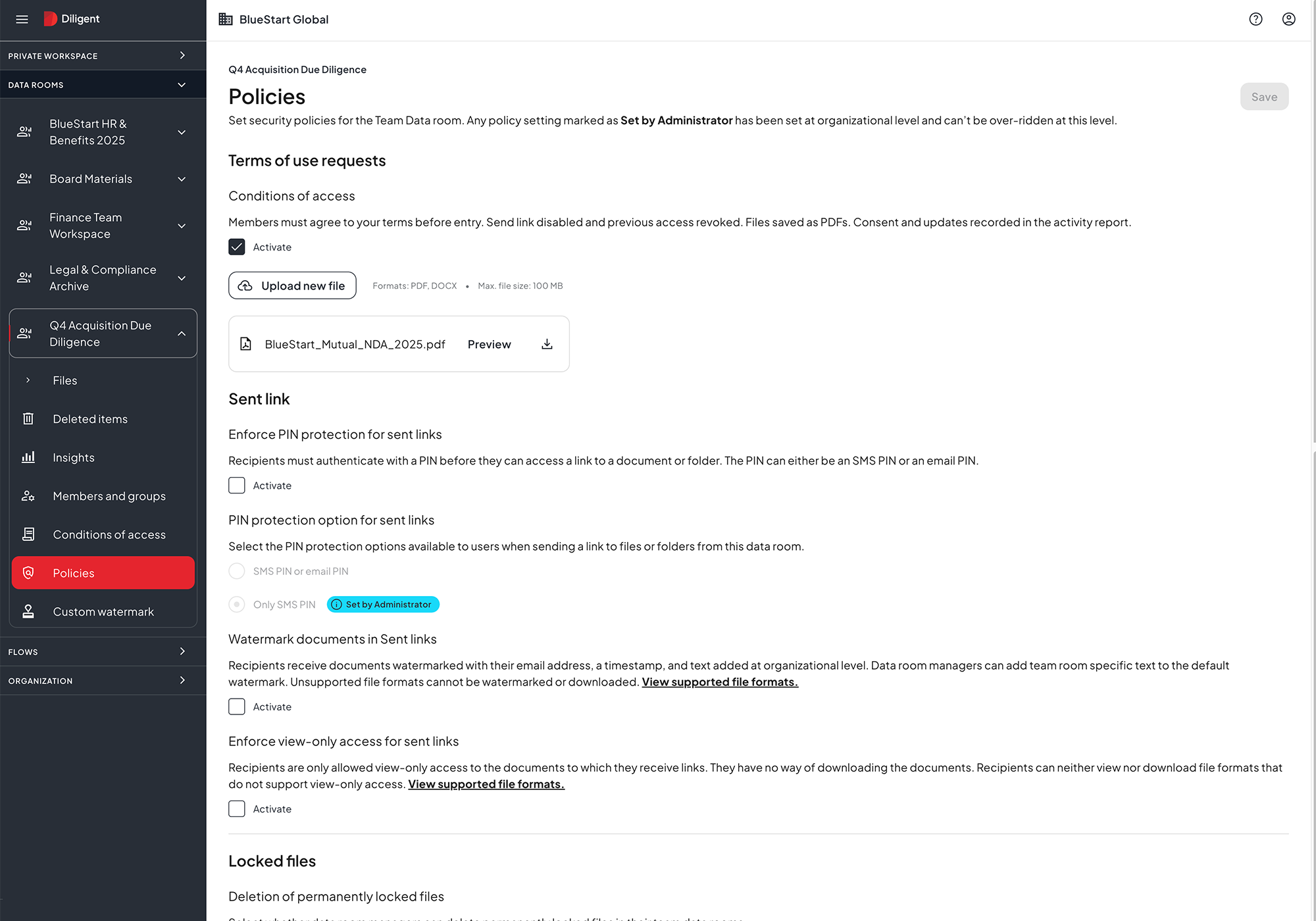
The platform supports an end-to-end policy lifecycle from creation and approval through distribution, attestation, monitoring, review and retirement. Version control, audit trails and real-time acknowledgment tracking produce the audit-ready documentation that Step 5 requires by design, not as an afterthought.
Diligent’s SOX Compliance capabilities use AI-powered control mapping to connect controls to regulations and auto-draft gap controls — directly accelerating control-matrix work in Step 4. Pre-designed frameworks, including SOX and COSO, provide starting points for organizations building or redesigning their control environment, while integration with ERP systems such as SAP, Oracle, and Workday enables the automated, continuous monitoring outlined in Step 6.
Together, these solutions create the integrated compliance architecture described throughout this guide: One where each new framework connects to existing infrastructure rather than requiring a parallel build.
The most effective compliance programs treat workflows as enterprise infrastructure, not department projects. When architecture is right, regulatory changes integrate smoothly, audit preparation becomes routine and audit committees receive quantified performance data instead of narrative assurance.
See how compliance teams automate multi-framework management and maintain audit-ready evidence continuously. Schedule a demo to get started today
A compliance program is the overall structure — policies, governance, staffing, training and oversight. A compliance workflow is the operational sequence that turns obligations into controls, evidence, monitoring and remediation. Strong programs often fail when the underlying workflow is unclear or inconsistent.
Start with the regulatory universe map from Step 1, then tier requirements by risk and enforcement exposure. Most large organizations prioritize obligations related to financial reporting, data protection, sanctions, and anti-corruption — control failures in these areas can result in immediate reporting and liability consequences.
Focus on trends and outliers, not activity volume. Committees expect coverage completeness, exception and remediation metrics, repeat findings and a clear view of material issues escalated outside the normal reporting cycle.
Use the common control strategy from Step 3: Define a single control catalog, map each control to multiple regulatory requirements and manage evidence once. Standardize control language using a recognized catalog, such as NIST 800-53, and keep the framework-to-control mapping centrally governed.
Review workflows quarterly at a minimum, with a full maturity assessment annually. Additionally, trigger reviews whenever a new regulation enters scope, an enforcement action in your industry signals a shift in priorities, or an audit produces repeat findings indicating structural workflow problems.
Ready to build compliance workflows that hold up under regulatory scrutiny? Schedule a demo to see how Diligent streamlines multi-framework compliance management.